6 ways to protect patient data in your eClinical and digital health applications
Patient data leaks is much more than patient privacy. Patient data leaks require a more complete approach to threat mitigation of patient data leakage, availability and data integrity attacks.
Since 2019, we see rapidly increased use of decentralized clinical trials, hybrid trials, digital therapeutics, mobile digital health apps and remote patient monitoring. Preventing patient data leaks should be the cornerstone of your patient-centric security policy. Here are 6 ways for preventing patient data leaks:
- Prevent leakage of any ePHI (electronic protected health information) from the mobile device itself, the management information system and or the hospital information system interface. Data loss can be prevented using DLP technology from companies like Fidelis Security and Digital Guardian without changing your systems.
- Ensure availability of your digital therapeutic back-end services, EDC or EHR application. When the application goes offline, it becomes easier to attack via maintenance interfaces, technician and super-user passwords and copy data from backup devices or access databases directly while the device is in maintenance mode.
- Ensure integrity of the data stored in the networked medical device, EDC or EHR system. This is really ABC of information security but if you do not have a way to detect missing or manipulated records in your database, you should see this as a wake-up call because if you do get hacked, you will not know about it.
- Ensure that a networked or mobile medical device cannot by exploited by malicious attackers to cause damage to the patient. Hospitals and point solutions for DCT and digital health do a poor job at enterprise security. You need to look at the hospital as a battlefield, the digital health app as a weapon and at patients as soldiers.
What we find is that the healthcare industry is by far the highest risk industry with respect to emerging threats and vulnerabilities and real attacks, not just the possibility of an attack, but real legitimate attacks, said Larry Ponemon, founder and chairman of the Ponemon Institute. “These organizations have been inept in implementing security processes, especially if we include issues around IoT, internet of things and internet of medical things. See cyber attacks on healthcare.
- Ensure that a networked or mobile medical device cannot by exploited by malicious attackers to cause damage to the hospital enterprise network
- Ensure that data loss cannot be exploited by business partners for financial gain. The best defense against data loss is DLP – data loss prevention since it does not rely on access control management.
Why do we have patient data leaks?
Just like theft, patient data leaks or is stolen because it has value, otherwise the employee or contractor would not bother. There is no impact from leakage of trivial or universally available information. Sending a weather report by mistake to a competitor obviously will not make a difference.
However – sending a list of 150 patients participating in a clinical trial, say for purposes of recruitment to another study is a clear case of unauthorized data transfer regardless of patient informed consent.
The financial impact of patient data leaks is directly proportional to the value of the asset. Imagine an insurance company obtaining patient data under false pretenses, discovering that the patient had been mistreated, and suppressing the information. The legal exposure could be in the millions. Now consider a data leakage event of patient names without any clinical data – the impact is low, simply because names of people are public domain and without the clinical data, there is no added value to the information.
Why people steal patient data
The key attack vector for patient data leaks is people – often business partners working with inside employees.
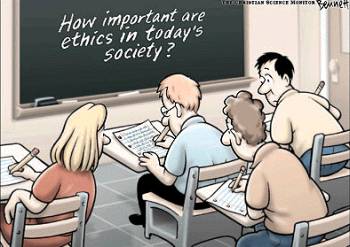
People handle patient data and make mistakes or do not follow policies. People are increasing conscious that information has value – All information has some value to someone and that someone may be willing to pay or return a favor. This is an ethical issue which is best addressed by direct managers leading from the front and by example with examples of ethical behavior.
People are tempted or actively encouraged to expose leaked/lost data – consider Wikileaks and data leakage for political reasons as witnessed in Israel several years ago in the Anat Kamm affair.
People maintain eClinical and digital health systems and make mistakes, leave privileged user names on a system or temporary files with ePHI on a publicly available Windows share.
APT42: Crooked Charms, Cons and Compromises
People design business processes and make mistakes.
Mistakes lead to vulnerabilities.
Consider a business process for a patient recruitment application in a hospital that enables investigators to retrieve patient candidates from the hospital EHR.
This process may have a vulnerability that can be exploited by malicious insiders or attackers using APT. APT (Advanced Persistent Threat Attacks) target a particular individual in a particular business unit.
Consider President Biden and Walter Reed Hospital and you get an idea for an APT attack.
Mandiant assesses with high confidence that APT42 is an Iranian state-sponsored cyber espionage group tasked with conducting information collection and surveillance operations against individuals and organizations of strategic interest to the Iranian government. We further estimate with moderate confidence that APT42 operates on behalf of the Islamic Revolutionary Guard Corps (IRGC) Intelligence Organization (IRGC-IO) based on targeting patterns that align with the organization’s operational mandates and priorities. See Spear Phishing and Surveillance
According to Wikipedia, APT attacks utilize traditional attack vectors such as malware and social engineering, but also extend to advanced attacks such as satellite imaging. It’s a low-and-slow attack, designed to go undetected. There is always a specific objective behind it, rather than the chaotic and organized attacks of script kiddies.
Why access control is not enough to prevent patient data leaks
One of the biggest problems facing organizations is lack of rigorous definitions for trusted insider threats, data loss and how to estimate potential damage from a data loss event. With a lack of rigorous definitions for data loss and trusted insider threats, it’s hard to benchmark with other companies and difficult to select a good set of data security countermeasures.
Referring to work done by Bishop – Defining the trusted insider threat
An insider can be defined with regard to two primitive actions:
- Violation of a security policy using legitimate access, and
- Violation of an access control policy by obtaining unauthorized access.
Bishop bases his definition on the notion “...that a security policy is represented by the access control rules employed by an organization.”
It is enough to take a glancing view at the ISO 27001 information security management standard to realize that a security policy is much more than a set of access control rules. Security policy includes people policies and procedures, good hiring practices, acceptable usage policies backed up by top management commitment to data governance, audit, robust outbound data security monitoring (or what is often called “DLP Light”) and incident response. Information security management is based on asset valuation, measuring performance with security metrics and implementing the right, cost-effective portfolio of security countermeasures.
A definition of trusted insider threats that is based on access control is therefore necessarily limited.
I would offer a more general definition of a trusted insider threat:
Any attack launched from inside the network by an employee, contractor or visitor that damages or leaks valuable assets by exploiting means (multiple accounts) and opportunity (multiple channels).
Using this definition, we can see that trusted insider threats is a matter of asset value and threat surface – not just access control:
- For example, employees in an organization that crunches numbers of weather statistics have nothing to gain by leaking crunched data – since the assets have no intrinsic value.
- For example, employee tendency to click on Microsoft Office documents can turn them into a trusted insider threat regardless of the access controls the organization deploys – as RSA learned recently.
RSA was hacked in the beginning of March 2011 when an employee was spear phished and opened an infected spreadsheet. As soon as the spreadsheet was opened, an advanced persistent threat (APT) — a backdoor Trojan — called Poison Ivy was installed. The attackers then gained free access into RSA’s internal network, with the objective of disclosing data related to RSA’s two-factor authenticators.
RSA is a big company with a big threat surface, lots of assets to attack and lots of employees to exploit.
The attack is similar to APTs used in the China vs. Google attacks from last year. Uri Rivner, the head of new technologies at RSA is quick to point out that that other big companies are being attacked, too:
“The number of enterprises hit by APTs grows by the month; and the range of APT targets includes just about every industry.Unofficial tallies number dozens of mega corporations attacked […] These companies deploy any imaginable combination of state-of-the-art perimeter and end-point security controls, and use all imaginable combinations of security operations and security controls. Yet still the determined attackers find their way in.”
Mitigating the trusted insider threat requires first of all defining whether or not there IS a threat and if so, finding the right security countermeasures to mitigate the risk.
This requires taking the threat of patient data leaks seriously. With the rapidly growing use of DCT, hybrid clinical trials, remote patient monitoring and digital therapeutics, we can no longer rely on access control and HIPAA compliance.
We need to consider threats to data integrity, availability and the vulnerabilities of trusted insiders.