Counterfeiting is old as money itself. Drug counterfeiting is no exception.
In this post, we’ll share an analytical approach that you can use to estimate the risk of drug counterfeiting to your drug products.
Why are Medicines a Target for counterfeiting?
Pharma is a highly regulated sector. Why do drugs attract counterfeiters?
- Fakes can be made relatively cheaply (at least as profitable as narcotics and at lower risk)
- Many countries, especially in the developing world lack adequate regulation and enforcement
- Even in the industrialized countries, the risk of prosecution and penalties for counterfeiting are inadequate
- The way in which medicines reach the consumer is also different from other goods: the end-user patient has little knowledge of the actual pharmacodynamics of the product.
Medicine counterfeiting is much more of a threat to public health than to company revenues.
Developing countries are the worst affected where regulatory structure is weaker and measurement and oversight is difficult; consumers in LDC’s often buy Rx drugs directly over the counter .
Non-branded generics are very widely counterfeited (e.g., ampicillin, paracetamol) • Prices vary widely across the world, and parallel trade is widespread, allowing counterfeit medicines to enter the supply chain.
People will not knowingly buy a counterfeit drug, but consumer detection is extremely difficult: price is not an indicator in insured markets. See this OECD report Pharmaceutical Counterfeiting: Issues, Trends, Measurement
We recently had the opportunity to work with a large generic pharmaceutical company examining innovative methods for preventing product counterfeiting.
In order to build cost justification for the project, we performed a quantitative threat modeling exercise that involved valuation of assets and analysis of a number of product counterfeiting threat scenarios.
The threat model is available on request – please contact us and we will be happy to send you a copy of the threat model and an explanation of how to use it in your own product counterfeiting scenarios.
Show me the money
The first question to be asked – what is the volume of financial damage due to drug counterfeiting?
What is the economic damage due to drug counterfeiting?
There is a dearth of scientific method in estimates of worldwide economic damage due to counterfeiting (7 percent of world trade seems to be extent of the mathematical model; as a result – the numbers range wildly from 10Billion dollars/year to 600 Billion Dollars/year).
The OECD reports that The economic impact of counterfeiting to the pharmaceutical industry is USD 17 billion/year.
This level of damage has generated a huge business in anti-counterfeiting technologies. There are hundreds of products and methods from RFID tagging to nano-particles that are being proposed as solutions (not even risk mitigation) to the threat of drug counterfeiting. Most of these technologies are not cost-effective and can be easily sidestepped (to make a fake product, a counterfeiter only has to make it look real – he doesn’t have to do the original research, development and manufacturing process).
What are the public health implications for patients?
Not surprisingly, because of the public health implications (how many men die from fake Viagra or women die from fake silicon breast implants), regulators like the FDA are stepping in. California is setting the gold standard like they did with consumer privacy protection – this time with a bill that would require a drug “e-Pedigree”.
Trying to combat the problem with supply chain traceability
The California e-Pedigree law (SB 1370) specifies pharmaceutical product serialization which “require the pedigree to contain the drug’s unique identification number established at the point of drug manufacture.”
When used through the supply chain, the e-Pedigree will help track and trace product, identify counterfeiters and enable consumers to authenticate the products they buy at the point of sale.
It’s impossible for me to estimate how much e-Pedigree will eventually cost (it only becomes mandatory in California in 2011) but it’s pretty clear that with all the packaging and information technology it’s going to be a pretty steep price for the drug supply chain.
In fact, the cost of track and trace has resulted in California dropping the law:
We applaud the California State Board of Pharmacy for their prudent decision to delay the implementation of E-Pedigree. While we certainly support the concept of using track and trace technology to limit the fraud and abuse of prescription drugs, the 2009 deadline was a logistical impossibility that lacked specificity for the affected parties. See delay of California e-Pedigree.
Modeling the threats of drug counterfeiting to patients
Instead of trying to solve an impossible problem, I decided to model a subset of the e-Pedigree. i.e. use of product serialization at the point of sale to the consumer in a pharmacy.
The notion of having patients call in a numeric token at the point of sale, in order to authenticate a drug they purchased, was first proposed by Johnston, a researcher at Los Alamos Laboratories. There are commercial track and trace implementations, available from companies like Optel traceability technologies.
How does a call-in numeric token work?
Patients would be able to authenticate the validity of a random, ID number printed on packages via a simple Web search query similar to the Google search page. Other channels might also be used – for example: sending a text message with a cell phone or a making a phone call to an automated voice response service. Customers with cell phone cameras could send a picture of the label over the Web to the system, which would extract the ID number using OCR and return a text message to the consumer.
When used by patients at the point of sale in the pharmacy, or at home; product serialization becomes a relatively low-cost, low-tech way to authenticate a product, since there is no supply chain integration required and the large number of consumer eyeballs calling in tokens is free to the manufacturer. I believe that there is also a viral marketing effect as people tell their friends about the system.
A Threat analysis of a drug counterfeiting countermeasure
We performed a threat analysis of the call-in numeric token method. Feel free to contact us and we will be happy to send you a copy of the threat model with an explanation of how to use it for your analyzing product counterfeiting scenarios. The threat analysis of the call in numeric token system was performed using the PTA (Practical Threat Analysis) methodology .
The risk analysis shows that by implementing the right security countermeasures, we can effectively mitigate risk and ensure confidentiality, availability and integrity of the clinical data and company revenue growth.
Threats are denoted (T-XX) and corresponding security countermeasures are denoted (C-XX)
T1 – Attackers may attempt to guess tokens
C01 – Make it difficult to guess by using a large, unpredictable collection of numbers; assure that there are at least 1000x more possible serial numbers than in a typical lot.
C02- Require additional data in the authentication query, for example, lot number.
C03 – Throttle multiple requests from a particular IP address
C16 – Block requests from known spammers using blocklists such as spamhaus.
T2 – Malicious outsiders may attempt to obtain tokens and reuse them on counterfeited products
C02 – Require additional data in the authentication query, for example, lot number.
C04 – The cost of buying legitimate products for the tokens is an economic disincentive
C10 – Use tamper-evident packaging, don’t print the token on external package.
C11 – Use query threshold of 3-4 that will prevent attackers from recycling stolen tokens
T3 – Trusted insiders may collude with criminals or competitors to obtain bottle numbers
C05 – Use a diskless interface box to feed the variable printer
C06 – Limit internal network access to the token database
C09 – Enforce strong passwords for system maintainers and recycle regularly
C15 – Require supply chain partners to sign NDA
T4 – Attackers may attempt to cause the service to become unavailable with a DDOS attack
C03 – Throttle multiple requests from a particular IP address
C08 – Do proactive patch management on token query server operating systems
C12 – Use commercial DDOS appliance above a certain query volume
T5 – Attackers may attempt to discredit the token query service with spoofing and/or phishing
C16 – Block requests from known spammers using blocklists such as spamhaus.
C17 – Operate the Web search site under the manfucturer’s corporate domain
C18 – Use HTTPS and provide a valid digital certificate for token query server
C19 – Provide branded and digitally signed widget for iGoogle
C20 – Provide consumer protection policy on query Web site
C01 – Make it difficult to guess by using a large, unpredictable collection of numbers, assuring that there are at least 1000x more tokens than in a typical lot size.
About Flask Data
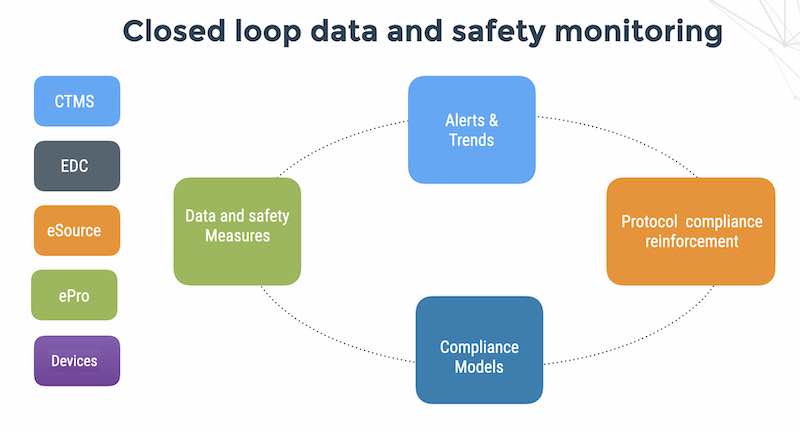
Flask Data is the industry-leading Digital CRO. We pioneered automated remote monitoring. Our customers consistently achieve over 90% patient compliance in decentralized trials with small clinical operations teams.
Most of our drug and device customers are doing pre-marketing trials. Some are doing post-marketing, real-world data, and PV (pharmacovigilance). Drug counterfeiting is a concern after you go to market.
If you want to learn more on how to estimate and mitigate your risk – contact us today.