There are some interesting analogies between cyber security and medical device clinical trials from a risk management perspective. Both areas are complex, vulnerable to human exploits and may result in loss of data.
Medical device trials are not exempt from unexpected human behavior.
Despite this concern, I find it significant that guidance for remote-risk-based monitoring of global multi-center clinical trials does not consider business controls for human resources, internal audit, and information security.
In this post, we consider the importance of study monitoring from a non-regulatory perspective of business risk.
Whether you are running a study on a wearable for monitoring diabetes, a home device for dispensing capsules or a devices for deep brain stimulation operated by a trained technician – you need to monitor for patient and physician compliance to the protocol.
In order to understand this point, consider the importance of understanding the psychology behind study monitoring. In this respect – both cyber and medical device clinical trials need to mitigate human vulnerabilities:
Study monitoring is a tough job – it has to deal with unexpected actions by trusted people in an environment assumed to be reliable.
In this article on insights in study monitoring, we consider automated remote monitoring as part of a premeditated program of business controls.
Let’s begin with the business case for automated study monitoring. There are 3 compelling reasons for sponsors to use technology for study monitoring:
1. Shorten time to market
2. Better ROI
3. Reduce complexity of data management
Phase II trials test for safety and efficacy.
Assuring on time/successful completion of the trial is critical to the product development cycle. Efficacy trials in particular benefit from remote monitoring, since they enable a sponsor to move from a reactive role of receiving reports to a proactive role using root-causee analysis and corrective action and shorten the time to market of a new product.
In Phase III trials, on-site monitoring is a significant expense for drug and medical device companies, and costs up to 30% of the total cost of the trial (See this report from HHS EXAMINATION OF CLINICAL TRIAL COSTS AND BARRIERS FOR DRUG DEVELOPMENT). Remote monitoring can help uncover issues in real-time, reduce avoidable rework and improve your ROI on study monitoring by as much as 50X.
Further down the road, Phase IV trials are the first time that a drug is tested in the real world and automated central monitoring is crucial to reducing the complexity of monitoring events and assuring data quality and safety in very large data sets of patients and many geographically dispersed sites.
Remote risk-based monitoring neglects 3 key business controls
In order to deal with unexpected actions by trusted people in an environment assumed to be reliable, we need a way of detecting these nasty things.
We can readily see that remote study monitoring of all sites, events and subjects, is good way of detecting “unexpected actions” like protocol deviations, entering dates in the future or not recording data in a timely fashion.
A solid remote study monitoring implementation includes 3 key business control activities which are often neglected in the context of the discussion of remote risk-based monitoring of multi-center clinical trials: human resources, internal audit, and information security.
I will highlight disconnects in each activity and recommend corrective action at the end of the article.
The HR (human resources) department
Ensuring employee loyalty and reliability is a central value for HR, which has responsibility for hiring and guiding the management of employees. Over time, organizations may sense personality changes, domestic problems or financial distress that indicate increased risks for employees involved with medical device clinical trials not being able to do their job properly.
Disconnect No. 1: HR isn’t accountable for the corporate brand and therefore doesn’t pay the price when trusted employees don’t do their job properly and contractors cook data. What can you do? Make HR part of an inter-departmental team to deal with the problem.
Internal audit
Clinical trial oversight should be part of an internal quality process that helps an organization achieve its objectives in the areas of:
- New product development
- Operational effectiveness
- Reliability of financial reporting
- Compliance with applicable laws and regulations
Auditors in the clinical trial industry say that regulation is their key driver for risk assessment and quality assurance of medical device clinical trials. EDC systems such as ClinCapture have free versions that enable small clinical trial teams to setup their own site and start managing data – using software with cool drag and drop user interfaces for building eCRF but lack automated monitoring controls.
Disconnect No. 2: Auditors have the job, but they have outdated tools and are way behind the threat curve. What can you do? Give your study auditors, remote monitoring tools and let them do their job.
Information security
Information security builds layers of firewalls and content security at the network perimeter, and permissions and identity management that control access by trusted insiders to digital assets, such as business transactions, data warehouse and files.
Consider the psychology behind wall and moat security.
Living inside a walled city lulls the business managers into a false sense of security.
Do not forget that firewalls let traffic in and out, and permissions systems grant access to trusted insiders by definition. For example, an administrator in the clinical trial group will have permission to log on to the EDC database and extract data using SQL commands. He can then zip the data with a password and send the file using a private Web mail or ssh account to a competitor.
Content-security tools based on HTTP/SMTP proxies are effective against viruses, malware and spam (assuming they’re maintained properly). These tools weren’t designed for data loss prevention. They don’t inspect internal traffic; they scan only authorized e-mail channels. They rely on file-specific content recognition and have scalability and maintenance issues. When content security tools don’t fit, we’ve seen customers roll out home-brewed solutions with open-source software such as Snort and Ethereal. A client of ours once used Snort to nail an employee who was extracting billing records with command-line SQL and stealing the results by Web mail. The catch is that they knew someone was stealing data – and deployed Snort as a way of collecting incriminating evidence, not as a proactive real-time network monitoring tool.
Disconnect No. 3 Relying on permissions and identity management is like running a retail store that screens you coming in but doesn’t put magnetic tags on the clothes to prevent you from wearing that expensive hat going out. What can do you? Implement real-time data loss audit using passive network monitoring at the perimeter. You’ll get an excellent picture of anomalous data flowing out of your network without the cost of installing software agents on desktops and servers. The trick is catching and then remediating the vulnerability as fast as you can. If it’s an engineer sending out design files or a contractor surfing the net from your firewall – fix it now, not 3 months from now.
Conclusion
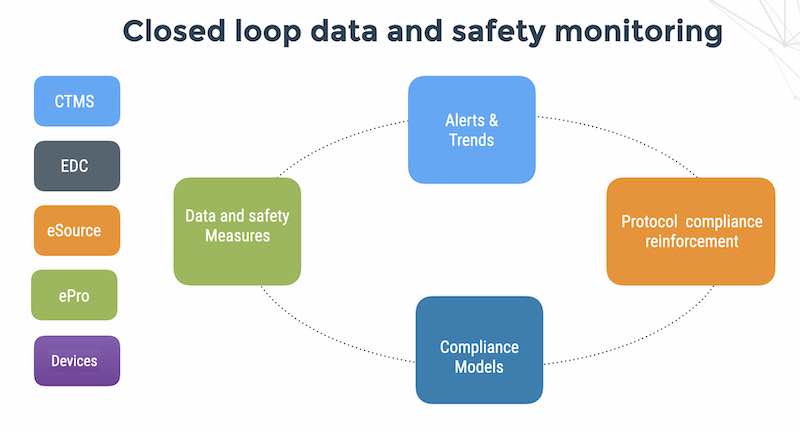
To correct the disconnects, you need to start with CEO-level commitment to quality. Your company should implement central monitoring as part of a premeditated program of business controls that revolve around the business and the human factors in your study.
– Soft controls: Values and behavior sensing, good hiring.
– Direct controls: Risk-based remote monitoring, information security
– Indirect controls: Internal audit
Danny is a physicist by training and entrepreneur who has started or served in key positions in 5 tech startups.
Danny has deep expertise in medical device security and patient privacy and has consulted to dozens of Israeli medical device companies in these areas. In his spare time, Danny volunteers at the Jordan River Village for children with serious diseases. He is a musician and plays in the JP Big Band.
Flaskdata.io | The team behind the world’s fastest patient compliance system Helping over 300 sites around the world and thousands of patients/month